CYBERSECURITY IN AN IOT ENVIRONMENT
November 2, 2017
One of the hottest new trends in the technology sector today is the Internet of Things (IoT). According to the McKinsey Global Institute the number of connected machines has increased by 300 per cent over the past few years. By 2025, the economic impact of IoT is estimated to range from US$ 2.7 trillion to US$ 6.2 trillion. Wikibon predicts that the value created from the Internet will be about US$ 1279 billion in 2020, growing annually at a rate of 14 per cent.
However, one of the key challenges that come up in such a connected world is that of security. Not counting mobile phones and traditional network devices like PCs, industry analysts forecast upwards of fifty billion network-accessible “things” by 2020. Given the level of access to personal information which today’s devices and apps have, it is easy to see how pressing the need for security is and how these challenges multiply with every additional connection formed.
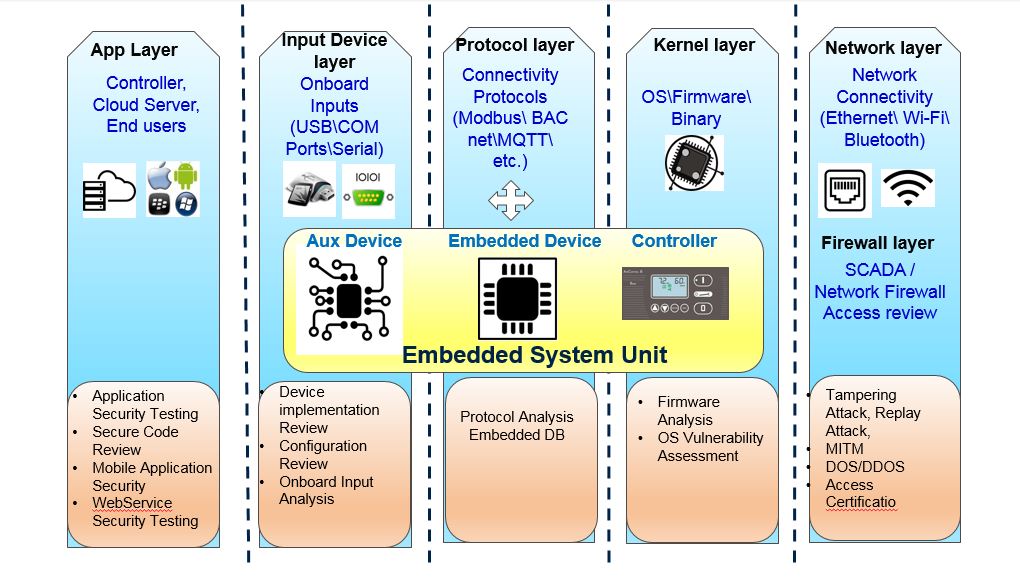
The following is a break-down of all the different aspects which need to be managed in order to build secure IoT networks:
- Secure Transmission of Data.
- Logical Access to Data Store- All databases need be protected from external access through strict firewall rules so that they are only accessible from mid-tier machines. Data also needs to be segregated in the database, using a unique tenant id. At the MQTT broker, broker data and traffic needs to be segregated between accounts using virtual machine segregation.
- Identity and Access Management– Confidentiality and integrity needs to be ensured through a role-based access control model and access control lists which follow the Principle of Least Privilege and are enforced through all the layers of the architecture.
- Vulnerability Management- An Independent certified security firm needs to perform remote vulnerability assessments, including network/host and applications.
- Patch Management- Specialized IoT hardware platforms like Arduino and Raspberry Pi Starter Kits come with all the goodies to help deploy IoT. However, often the OS/Packages/Protocols used are open-source where one has to wait for a long for patches and upgrades. This leads to potential security risks.
- Protocols for protecting data in motion and data at rest- IoT systems are often used to gather sensitive data such as medical biometrics, personal schedules, and inventory and supply chain information, etc. Even when system is not gathering any data, it stores enough contextual data that can be very useful for analytics tools and cross-reference systems. There is a Range of protocol that needs to be followed when interconnecting IoT devices so as to ensure security of both data in motion as well as data at rest.
- Multiple user interfaces– With many devices having multiple user interfaces, there is a lot of potential for vulnerabilities and either partial or fully compromised IoT networks. Some of the common vulnerabilities due to faulty user interfaces are:
- Use of unauthenticated requests to perform actions (for example, reconfiguration, data retrieval, management functions, etc.)
- Ability to perform unrequested firmware upgrades
- Command injections
- Buffer/heap overflows
- OWASP’s List of the Top Ten Web Vulnerabilities
- Cloud Backend Infrastructure. IoT systems Cloud infrastructure includes a back-end cloud service, depending on the category of the device. This cloud service can be accessed through a smartphone app or a web portal and this gives rise to certain vulnerabilities. Unfortunately, many of these services allow users to chose a weak password, have unsecure password recovery methods or reveal too much information during the recovery process. Some of these cloud services have logical errors, which can allow an attacker to obtain sensitive customer information or access devices without authentication. They also contain common management console vulnerabilities, including those listed in OWASP’s List of the Top Ten Web Vulnerabilities.
To help tackle these risks, we at Capgemini have developed a layered approach towards ensuring IoT solution security. To find out more about this unique approach, download the whitepaper here

 English | EN
English | EN 
