THE NEXT ERA OF IDENTITY
July 24, 2018
Digital identity is currently undergoing a paradigm shift to improve the privacy and trust of online identities. A good example is the GDPR which enables citizens in the EU to return the control and management of personal data and identities to the individual.
Another example is the way how we look at social media in this user-centric era. The Facebook–Cambridge Analytica data scandal started the discussion about personal data and might change the way we use social media nowadays.
These are some examples which affect the way we handle our identities and stimulates the shift towards a new model: the self-sovereign model.
So what is self-sovereign identity?
Self-sovereign identity is the concept that people and businesses control their own identity and store related data on their own devices. This data is only shared with those who need to validate it, without relying on a central repository of identity data.
This digital concept is very similar to the way we keep our non-digital identities today. We keep documents like passports, birth certificates, diplomas etc. at home and store them at a secure place. We share these documents when asked for when, for example, applying for a job. In this way the candidate can proof its resume based on the information (claims or credentials) in the diploma. The company verifies the diploma with the University the applicant studied.
Self-sovereign identity takes this even one step further by using the following principles:
– User is in control of the claims and these are not stored in a central repository; The user keeps all its personal information in it’s own wallet.
– Peer-based relationships; 1-1 relations.
– Unique identifier replaces the username/password;
– Share what’s required, but not more;
– Interoperability; Interconnect with multiple platforms.
Under the hood
It might all sound a bit futuristic but the self-sovereign identity concept and the required technical components are under development already
A. Decentralized IDentifier (DID); The digital ID (or Private Key) representing the Owner by leveraging the blockchain.
B. Digital Wallet (or Decentralized Key Management System); A system to store and manage the DID’s of the owner.
C. Verifiable credentials; Claims and personal related data (drivers license, passport etc.) used to proof issued third party credentials.
D. Universal Resolver; A unified mechanism used to resolve any kind of DID.
The following diagram illustrates the cohesion between the components:
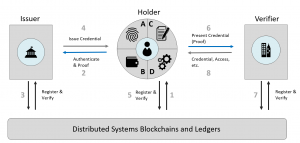
The first step for a user is to register its DID on a Distributed Ledger. By doing this the user is able to authenticate and request a claim (for example a passport). The issuer verifies the presented proof of DID and issues the credentials to the user. The user holds this credentials in his digital wallet and can present this to other parties to retrieve new credentials or to consume services.
Some Decentralized Identity systems exist nowadays like Sovrin, uPort and Veres One. These projects are still under development but the adoption of some of them already started. Microsoft also announced compatibility with Sovrin and decentralized identifiers at Consensus 2018.
What are the challenges?
The Decentralized concept involves some major changes to the way we work nowadays which also brings some challenges to the table.
Some of the typical challenges are:
Scalability
Scalability is one of the most common challenges with every technological shift. How are we able to distribute this new model globally and how do we guarantee the performance?
Adoption & Use
Above all, this new way of working requires a change in the mindset of a user. A user is now responsible for its own digital identity instead of relying on other parties taking care of their personal ID
The easiness of use is key in the adoption of this technology. The way a user handles his credentials and secrets and how he or she can interact with others is essential in this model.
Key management
Key management is one the open issues in this area. How is a user able to recover access to his or her digital wallet?
Wrapping it up
Although, this digital concept is still under development, I am pretty sure this will be a game changer in the near future. This new era of identity will give back control of the identity to the user, handling the identity like we handle our non-digital identities today.
This will lead towards an era where users gets control of their identity and decide what personal information is shared with whom based on one-to-one relationships.

 English | EN
English | EN 