HOW MANY PASSWORDS ARE WE JUGGLING WITH TODAY?
December 7, 2015

Looking for a guaranteed job for the next decades? Worried about the future job of your children? Advise them to go and study IT security and specially authentication concerns. Be sure that for the next decade, this will be one of the main IT problem, companies have to cogitate on.
Some history. For years, more than 95% of Fortune500 relied mainly on Microsoft Active Directory authentication system (to which we can add around 90% of medium and large enterprises all over the world). As a legacy of the 90’s, we more–>come from a 100% on-premises IT infrastructure mindset hegemony where AD is the static basements. This was a time where all business digital systems used to come with their own Directory and their own authenticating mechanism. All those, totally segregated, satisfying thus each need independently. Then came the Cloud and the iPhone uprising, that changed the corporate world.
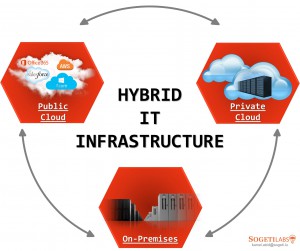
Expected by many, the “Big Day” will not occur. Revolution of the whole world where everything will be replaced by either Amazon Cloud, Mac World, or Google land… will not happen. We all agree to correct this manichean thoughts by a more challenging approach:
Hybrid
The constantly increasing acceleration of innovation, the empowerment of users request more agility than ever. That’s why, we must select the best for each piece of our Information System, regardless of compatibility issues.
Any company from any sector uses in its business as usual several applications: e-mail, ERP, CRM, web apps, groupware, e-mail, ticketing tools, and inventory developed by different editors and hosted via different architectures. Hybrid will become a standard. Moreover, empowered users refuse to pay the price by juggling with tens of passwords and accounts.
Let me tell a bit about my life. A few months ago I booked a holiday to NYC for the entire (6-member) family. I was told that Airbnb is a great alternative to expensive and impersonal hotels. So I browsed on the Airbnb website, totally persuaded that I’d have to create, yet another, new account on these kind of websites, and, I was strongly and nicely surprised to find out that a Facebook account could be used to authenticate, avoiding thus the creation of new account. Days after, I discovered that it was the case for most of the website services now. Originally created to get dates for a shy teenager, Facebook is to become a SSO for consumerists. What a big trend!
So each time companies migrate or integrate new systems, they will have to face out the same authentication issues, more and more.
During another thrilling episode of my life, I got my login accidently erased from AD.
Helpdesk: “Cannot login anymore Kamel? So you cannot do anything! When we fix your authentication issue, you will be able to work again”.
My answer: “No way! I mainly use Office and web-based apps, since my data is on the cloud, I just need new platform so I can go on working. Ok?”
Despite my 20 years of expertise, I can act like a basic end-user. So comfortable.
Adding ”… and by the way, security concerns are not my business. I do not want to hear any complaining about how GPOs issues are tricky and painful to fix. I just want to work now!”
So, do we have to consider Active Directory – an authentication directory – as a SPOF for Business? No way! Don’t want to minimize the role of a global directory but it is simply a core IT service. No more.
For many reasons, Active Directory is not the answer for everything. Since AD was designed for an On-premise static Microsoft integrated world, it must be considered as a component of the problematic more than a key solution.
New opportunities. I see plenty of new cloud identity players, each one claiming to be the best and the only to be fully compliant with everything on earth. How can we guarantee to be fully compliant while we do not even know which future system we need to comply with?
The myriad of systems, the diversity of the web-based technologies, the emergence of a multitude of new ways of working literally put an ultimatum on CIO’s head, called SSO.
While business (galvanized by DevOps fresh air) is asking the CIO for (yet another) new system, specifying their want the easiest way for end-users (no additional passwords..) based on the cheapest and the more scalable PaaS (hybrid), the CSO asks in parallel for more security and resists against risks of new lake of security. We are in. Authentication issues that must comply and satisfy with several parts.
Database into the cloud talking to Web Servers which host web app accessible from the LAN by internal users but also from outside users.
This is just the beginning. In addition, companies will face massive introduction of web 2.0, wearables, IoT into their own business.
After the Command Line Interface
And the Graphic User Interface…
We now have the User-with-Things Interface
There will be even more authentication issues to handle. I promise you, Your grandchildren will also have plenty of opportunities in IT.

 English | EN
English | EN