STRIKING THE RIGHT BALANCE BETWEEN SECURITY AND CONVENIENCE
January 13, 2015
 Private data of virtually anyone can be found on the web, given the average of around 26 online accounts that every person has on different websites. But we don’t do a good job protecting those data. Unfortunately, quite often “we” means you and me, that is the users, not the IT people. For those many accounts, we tend to use only a limited set of passwords, often bad ones too – easy to guess if an attacker happens to know some basics about us, or just plainly easy to guess.more–>
Private data of virtually anyone can be found on the web, given the average of around 26 online accounts that every person has on different websites. But we don’t do a good job protecting those data. Unfortunately, quite often “we” means you and me, that is the users, not the IT people. For those many accounts, we tend to use only a limited set of passwords, often bad ones too – easy to guess if an attacker happens to know some basics about us, or just plainly easy to guess.more–>
Using identical passwords has the major drawback that a hacker who succeeds in getting his hands on the login details on a website you hardly ever frequent, could use that information to gain access to your files on Google Drive or photos on iCloud. In theory, the solution is simple: always use unique, long (yes, size matters) and practically random strings of characters as your passwords. But then again, these tend to be rather hard to remember, so not so convenient. The choice for identical passwords was a choice for convenience. Us, users, are very keen on convenience!
In search of that convenience, some companies are looking at biometrics: Apple’s Touch ID allows you to authenticate with a simple push on the button through fingerprint recognition. This too may be deceived, however. A German researcher has recently proved that some high quality pictures of hands and fingers were enough to construct the entire fingerprint, which could then be used to gain access to systems relying on it for authentication. The same researcher claimed that he can fool iris recognition hardware in a similar way.
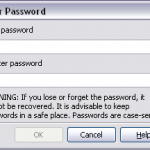
As randomness and chance play an important part in security, multiple keys should always be preferred over a single (be it biometric) key. For convenience’s sake, many people have turned to password managers to keep their passwords organized. Password managers are standalone applications or browser plugins who keep a record of your passwords, randomly generate and store new ones as needed, and enter them automatically for you when you need to authenticate yourself. This only works well of course if the contained passwords are properly secured and if websites and applications are designed to properly interact with them.
Although more pragmatic – perhaps to a degree defeatist – approaches have been proposed as well, password managers have the advantage that in time, they may also be used to store public keys of our contacts, which can be used to decrypt the signed messages they send us. Indeed, there is still a lot of room for improvement in securing data traffic! In the emerging Internet of Things a lot of personal information is sent over wireless networks so it’s important that this communication cannot be read when intercepted.
2015 will be an interesting year to see developments in that area as well: the initiative Let’s Encrypt, which will provide free TLS/SSL certificates, should encourage websites to use safer connections the whole internet will benefit from.
In a recent article, a Dutch science journalist has called for using more “digital chaff” to protect our data traffic. This involves sending around encrypted random data to distract the attention of hackers looking to steal actual private data and thus discourage them to go through the trouble of finding weaknesses as they risk to put a lot of effort into something that might not yield any useful results at all. While this will need more publicity to be broadly adopted by the online community, this should be possible to organize at a corporate level and adding an extra layer of security without reducing convenience.
That is key because if convenience is not something one strives for in security, users will always find convenient ways that are actually insecure.

 English | EN
English | EN 