Andy Grove famously wrote – ‘Only the Paranoid survive’
The message still makes sense and the only true solution to attacks (I mean her ones on our Digital Assets) is eternal vigilance. Having said that, there is one particular challenge in CyberSecurity whether you implement the latest and best of breed security protocol and systems; it is the ever evolving kaleidoscope of both the landscape and the actors (read threats). Landscape changes every few weeks or months as new policies are implemented, but the upstream impact of tweaking your Security architecture is not done and … ergo an involuntary lapse between good intent and good protection. The actors (hackers and attackers) keep changing their MO every fortnight or even week as they crowdsource vulnerability. It’s very difficult for even the best software firms to beat crowdsourced innovation especially when a lot of it is done for the kick and not for money. So when landscape changes and actors morph, the natural solution is that Security be dynamic and not static.

Prominent Lapses in Security
Existing cybersecurity architectures and operating models cannot cope with the changes in architecture which are driven through when customers migrate to public-cloud platforms. Why? Misconfiguration is a greater challenge for the customer, in fact most public cloud providers have much better security than what traditional datacenters can provide. Attack on the public cloud infrastructure will be very rare instance as its built for defying such attacks and is on a high alert all the time.
What is Security as Code?
Simply put – SaC – is a model where you define your Cyber security policies as Code and not as a static rule.
Three areas of focus for Security as Code:
- Security Testing
- Vulnerability Scanning
- Access Control and Policy Management
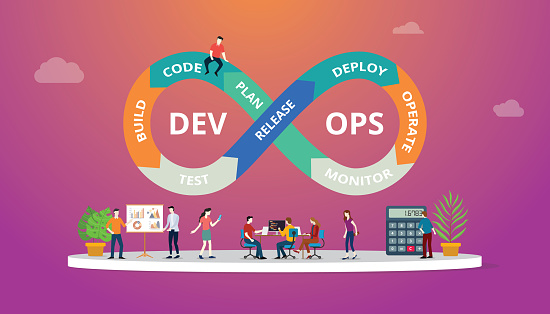
Security as Code can programmatically refer to various routines, subroutines and scripts. Imagine a scenario where because of the popularity of DevOps in enterprise business, there is continuous development. Security as Code represents the next evolution of DevOps–a development where security is fused into the development process.
Security as Code best practices include:
- Monitoring functions
- Routine security policy checks
- Automating feedback loops
- Automating scans and security testing
- Executing scripts
More information? https://www.sogeti.com/services/cybersecurity/

 English | EN
English | EN 