IOT HAS A NEW SECURITY STANDARD
September 27, 2023
We live in a world where the security of our networking and computing infrastructure is of prime important.
Our financial systems, our systems of commerce and transportation, they all require protection against nefarious actors.
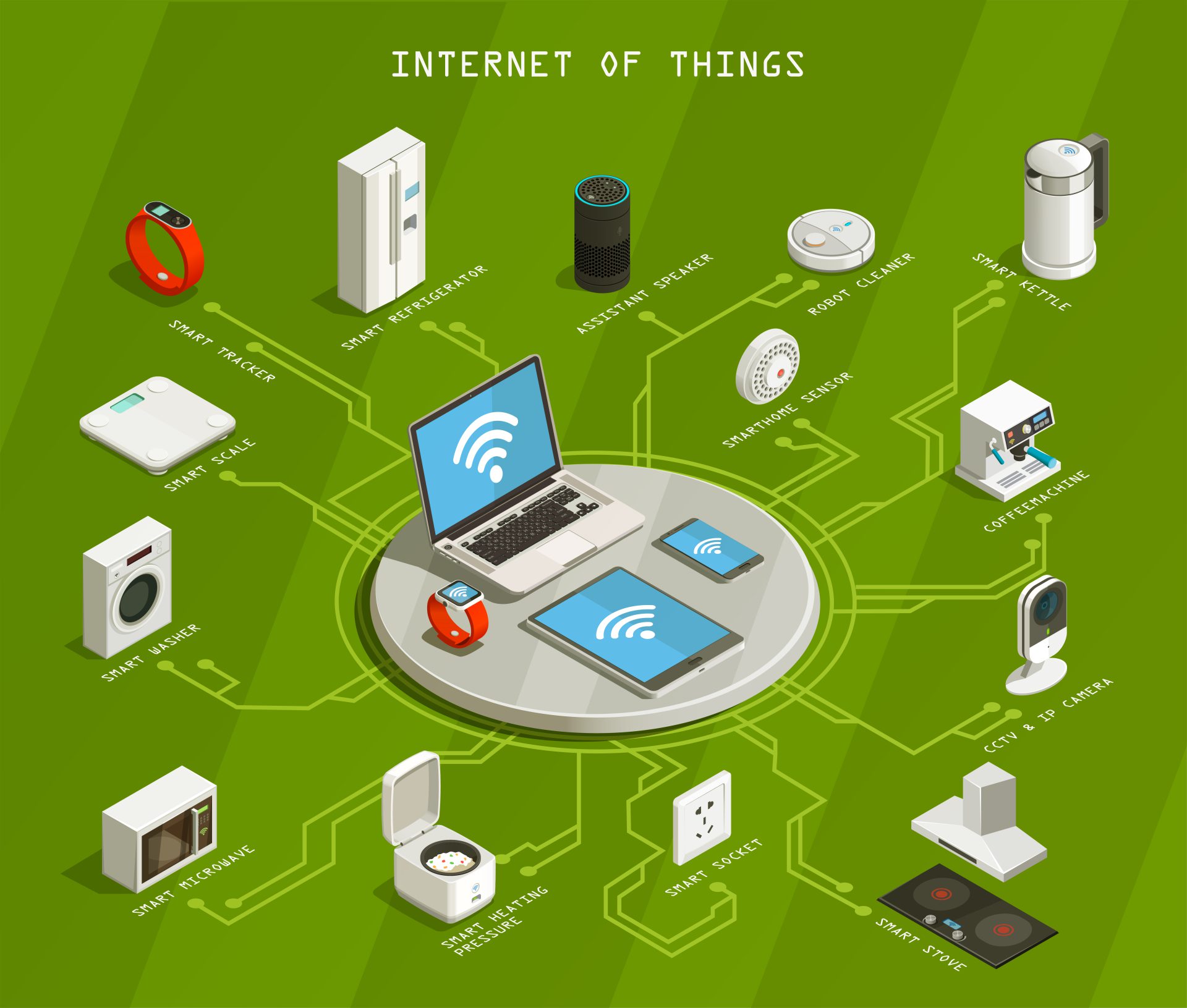
There has been, however, one area of IT infrastructure that has lagged in providing the levels of security we have come to expect in other systems: the Internet of Things (IoT).
In the early days of IoT, security was virtually non-existent. Unencrypted channels, lack of passwords (or static passwords), backdoors, easy access to configuration data–all these, and more, were the “standard” in early devices.
Some of these weaknesses, it could be argued, were necessary to further rapid adoption of IoT, as was the case in the early Internet. But, unlike the most of the Internet, IoT devices are connected directly to devices which, if control can be taken over by bad actors, could be used to cause great harm.
IoT-controlled refrigeration equipment used to store medical supplies and drugs; smart electricity substations and generation plants; nuclear reactor control systems (a real-world case).
The early IoT landscape was a bit of a wild-west.
“Despite continued security problems, the IoT will spread and people will become increasingly dependent on it. The cost of breaches will be viewed like the toll taken by car crashes, which have not persuaded very many people not to drive.”
Richard Adler
Thankfully, the industry has not taken the view that IoT breaches are just the cost of doing business, as early savants thought.
Today things are better, but the solution to providing IoT security has been rather ad-hoc–until now.
Following a set of regulations signed into law in the United States in 2021, the National Institute of Standards and Technology developed NISTIR 8425, a standard for IoT security.
The new standard–optional for US manufacturers, unfortunately–is gaining acceptance and generating productive discussions in other countries. By 2024 or 2025 the European Union will require that such devices adhere to a strict set of security standards.
One feature of the US standard is that IoT devices will have to contain a label indicating compliance the standards (rather like a UL or CE markings). In addition–in a rather surprising and clever requirement–these labels will contain a QR code that the user can scan to determine if the compliance is still valid for that product.
We can hope that market forces will compel IoT systems manufacturers to adhere to the new standards as soon as possible, forcing non-compliant and insecure systems out of the market.

 English | EN
English | EN 